SSL Certificates are small data files that digitally bind a cryptographic key to an organization’s details. An organization needs to install the SSL Certificate onto its web server to initiate a secure session with browsers. Once a secure connection is established, all web traffic between the web server and the web browser will be secure.
By default, all NSX Manager Appliance has a Self-Signed certificate and it is not recommended to keep same certificate in your Production Infrastructure. In this blog I will explain how to Create, Sign and Replace the certificate of NSX Manager with you Organization Certificate Authority Server.
Prerequisites
- To Start with we need a Microsoft Certificate Server and The Certificate Template which supports vCSA, This link will help to Install and Configure a MSCA server and to create a certificate Template.
- First, to manage certificates in the NSX Manager, you must go admin URL
Generating Certificate Request
Login to NSX Manager by using IP Address or FQDN
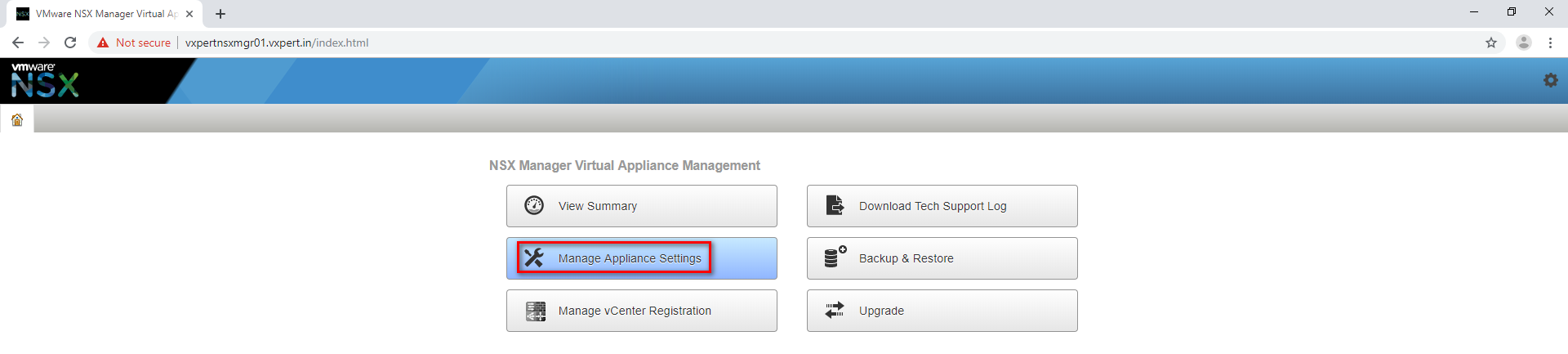
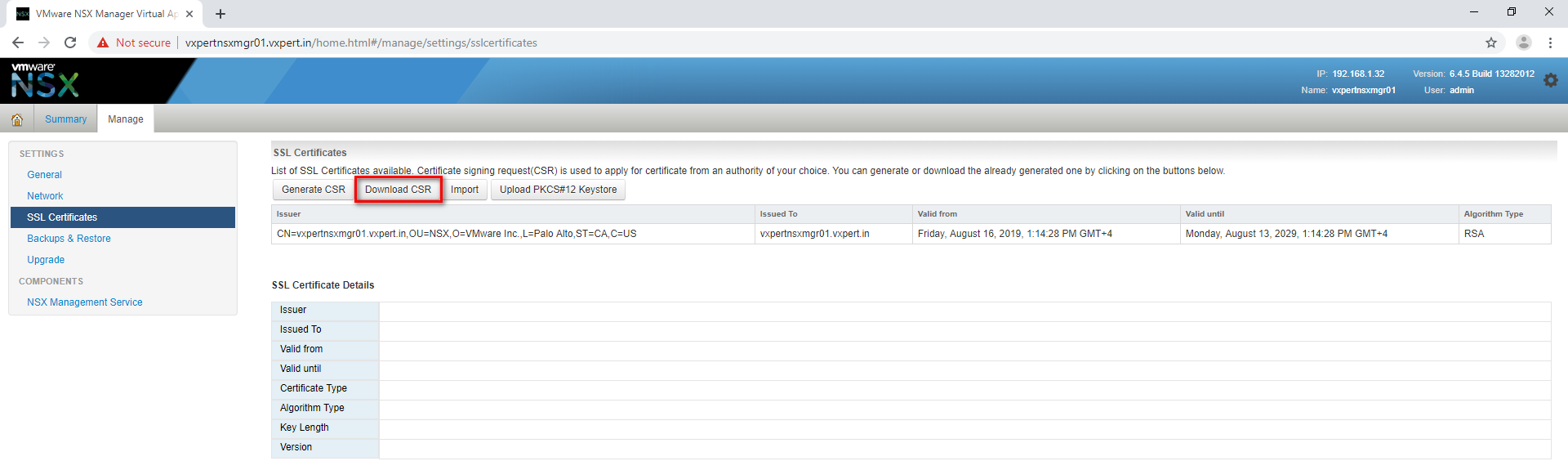
Click Manage Appliance Settings – SSL Certificates
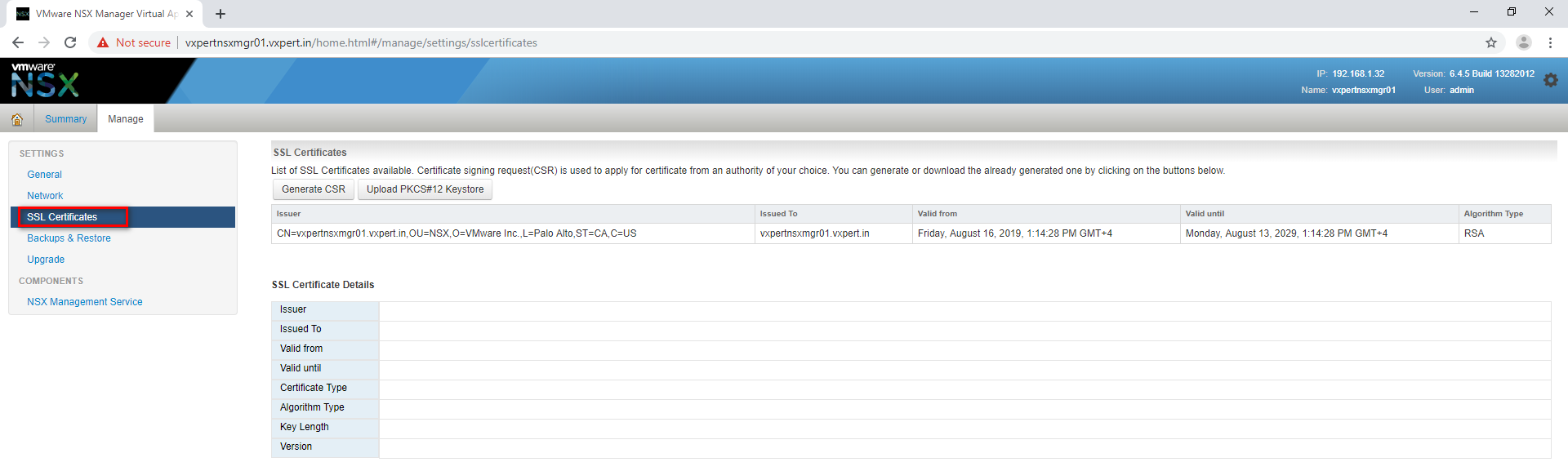
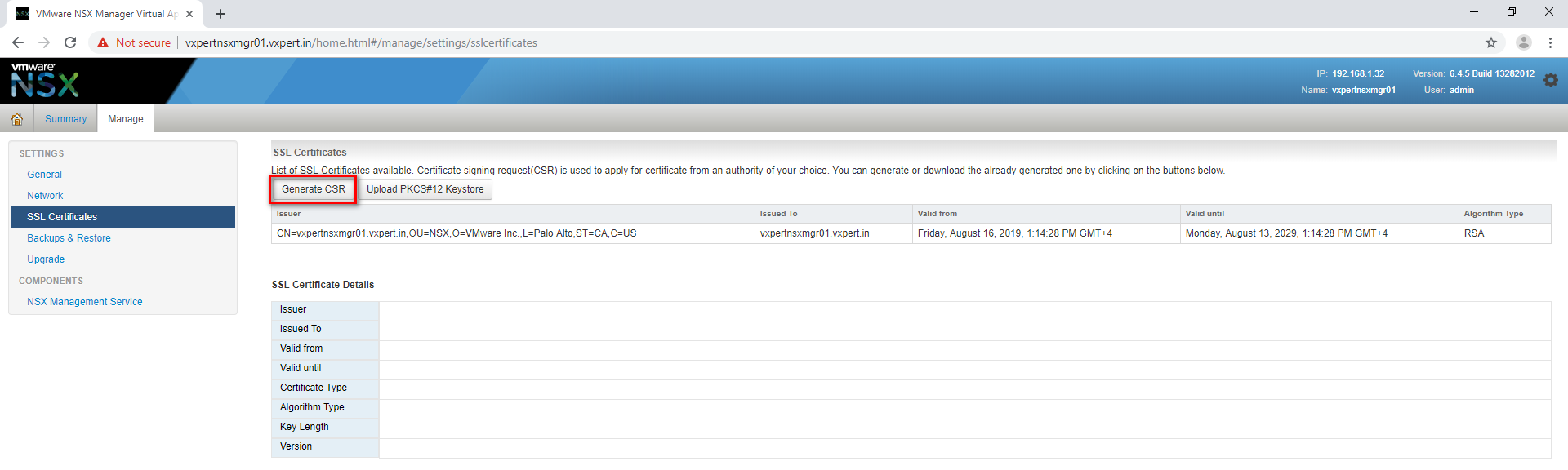
Click Generate CSR to create a new CSR for NSX Manager.
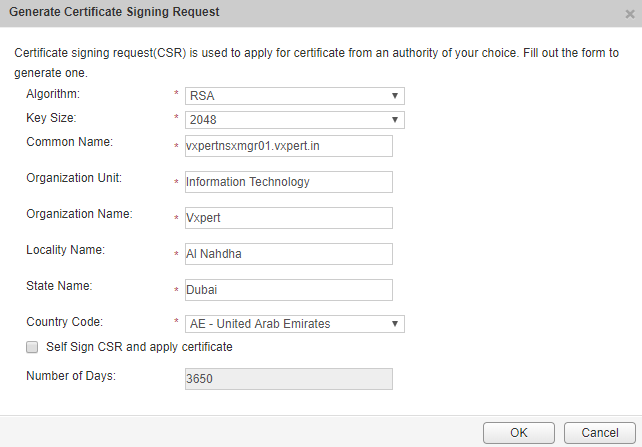
Provide the required field with details shown below and click OK
Download the newly created CSR to proceed with Signing
Sign the Certificate with CA
After the certificate request is created, the certificate must be given to the certificate authority for generation of the actual certificate. The authority presents a certificate back, as well as a copy of their root certificate, if necessary. For the certificate chain to be trusted, the root certificate must be installed on the server.
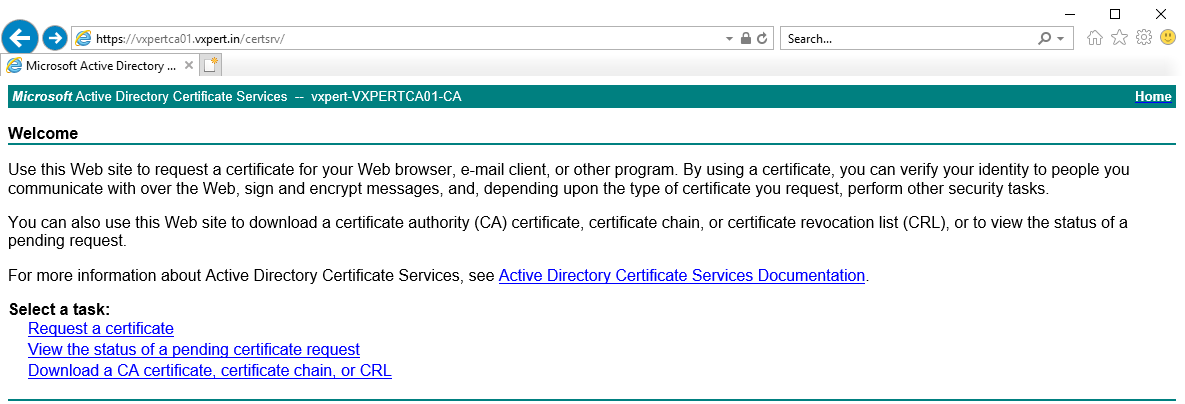
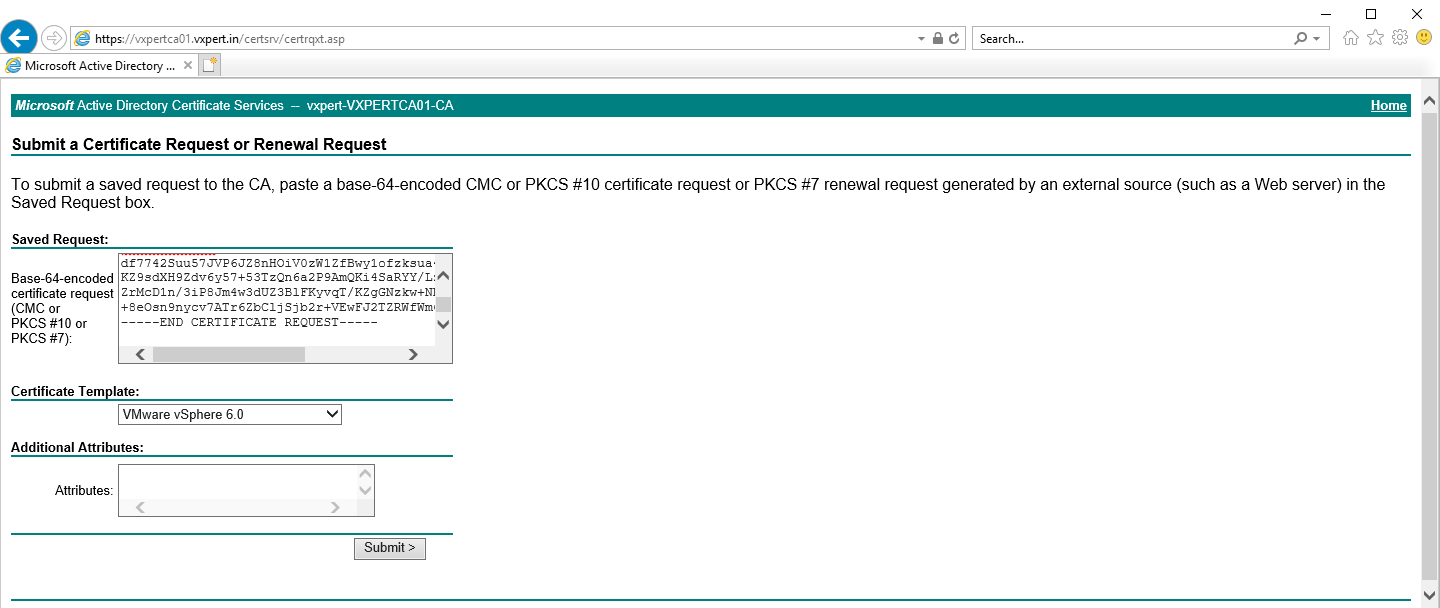
Log in to the Microsoft CA certificate authority web interface. By default, it is http://servername/CertSrv/
Click Request a certificate
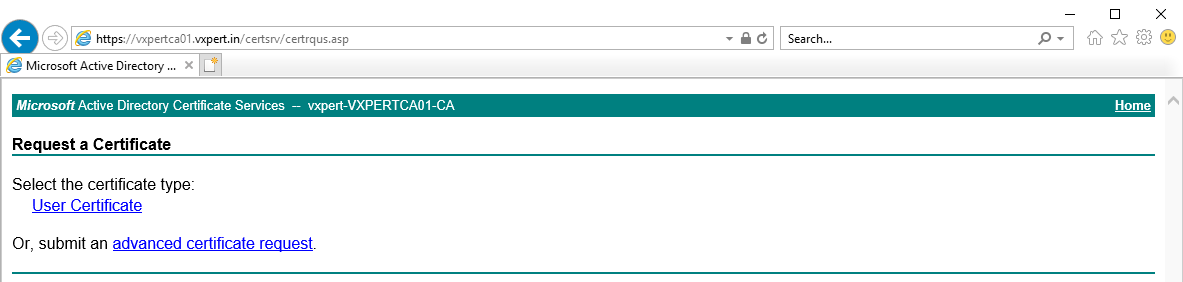
Click Advanced certificate request
Click Submit a certificate request by using a base-64-encoded CMC or PKCS #10 file, or submit a renewal request by using a base-64-encoded PKCS #7 file
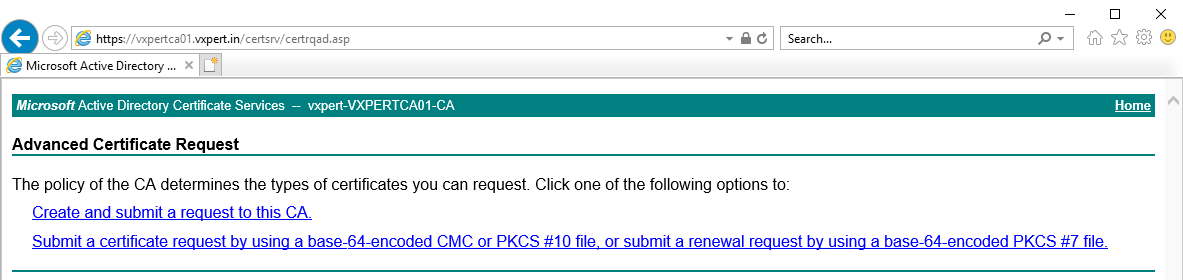
Open the certificate request (NSX.csr) using a text editor, Copy the content from —–BEGIN CERTIFICATE REQUEST—– to —–END CERTIFICATE REQUEST—– into the Saved Request box. Please, be sure to select “VMware vSphere 6.0” in the “Certificate Template”. Click Submit.
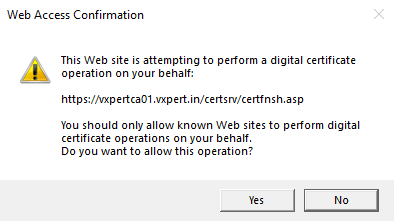
Click Yes to confirm
Once you administrator approves the request you can download the Base 64 encoded certificate chain on the Certificate issued screen, this will have new certificate as well as all the certificate of the issuing authority chain
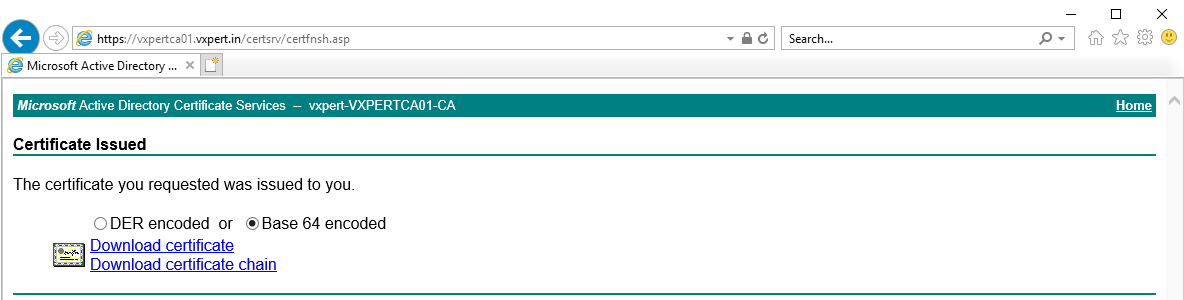
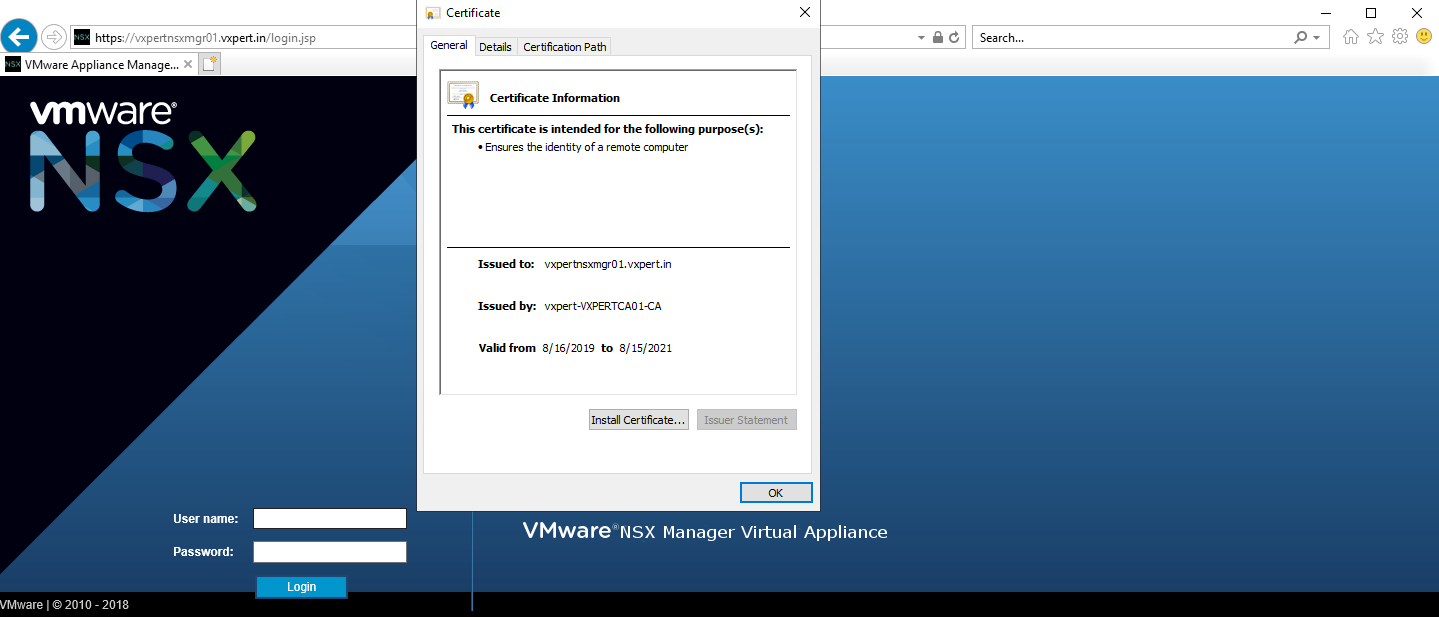
Save the certificate as vxpertnsxmgr01.p7b filename, Open the certificate and check the parameters you have provided is correct or on not.
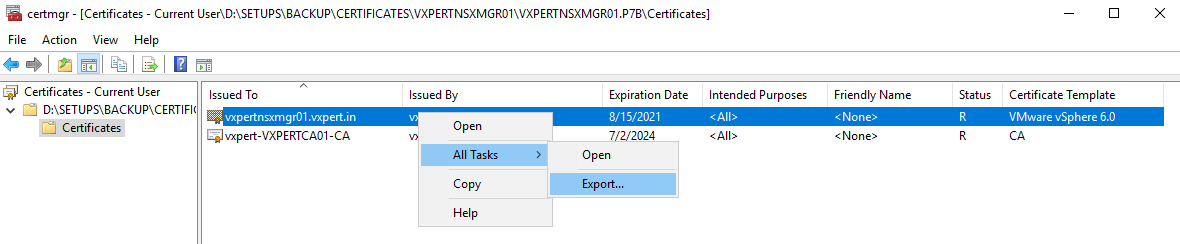
Launch your newly created chain file and browse to Certificates
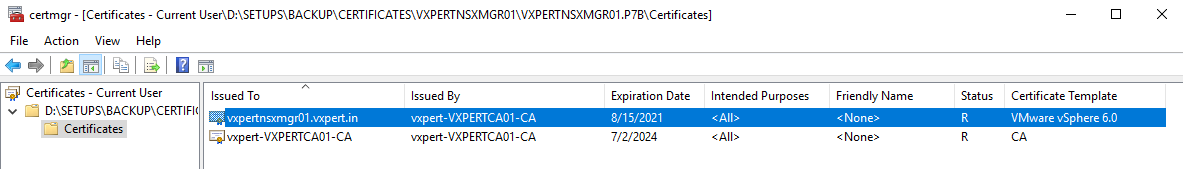
Right click on vxpertnsxmgr01 certificate and All Tasks – Export
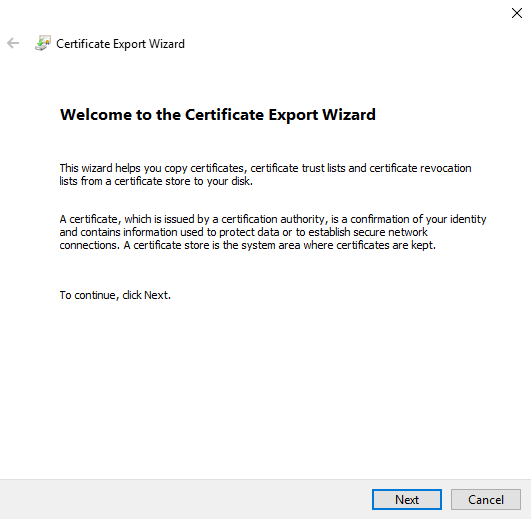
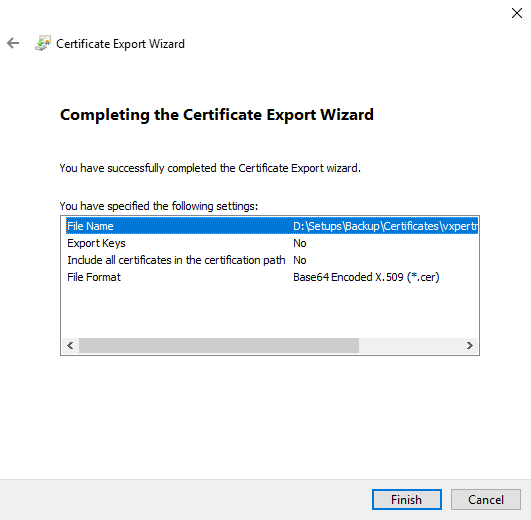
Click Next on Certificate Export Wizard
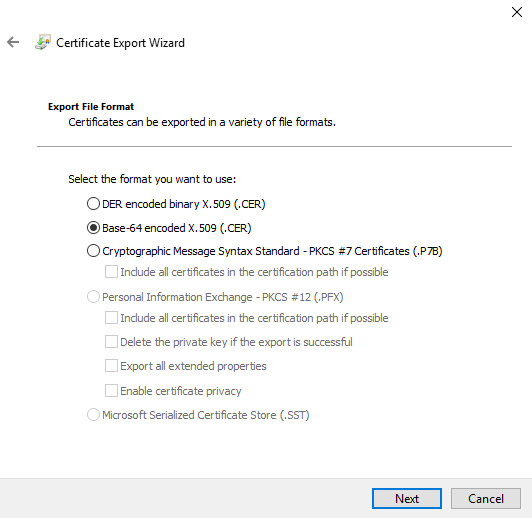
SelectBase-64 encoded X.509 (.CER)and click Next
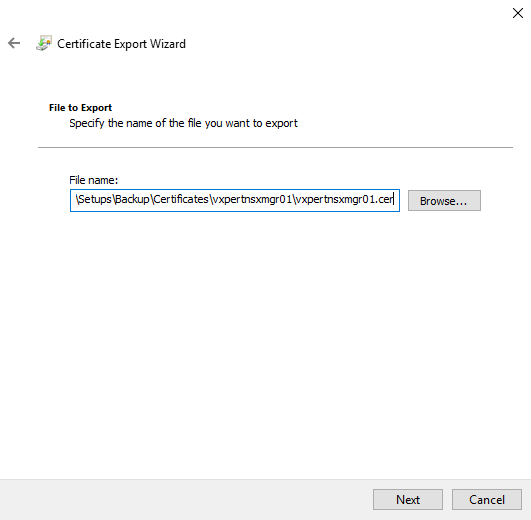
Browse and provide location to save the certificate file and click Next
Click Finish to complete the certificate export
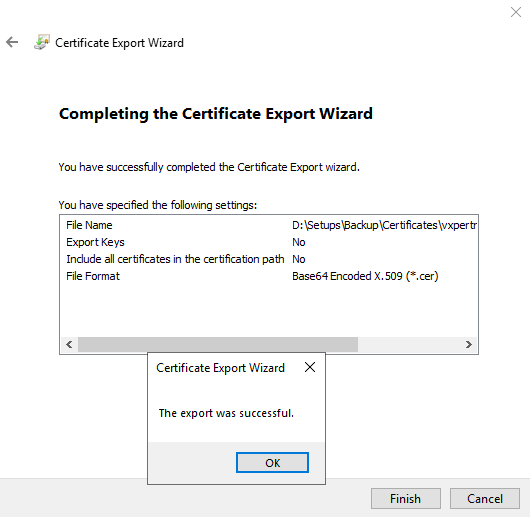
Repeat the same steps to export the root certificate also.
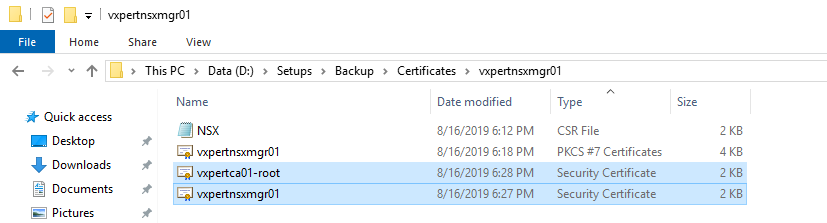
Combine the certificate chain (vxpertnsxmgr01.cer and vxpertca01-root.cer) by opening the file in notepad and save it vxpertnsxmgr01chain.cer format.
Installing Certificate on NSX Manager
Once the certificate is created login to NSX manager console again and Navigate to
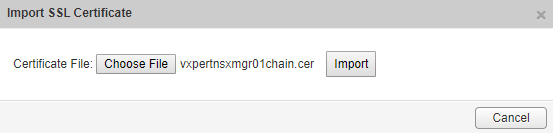
Click Manage Appliance Settings – SSL Certificates – Import
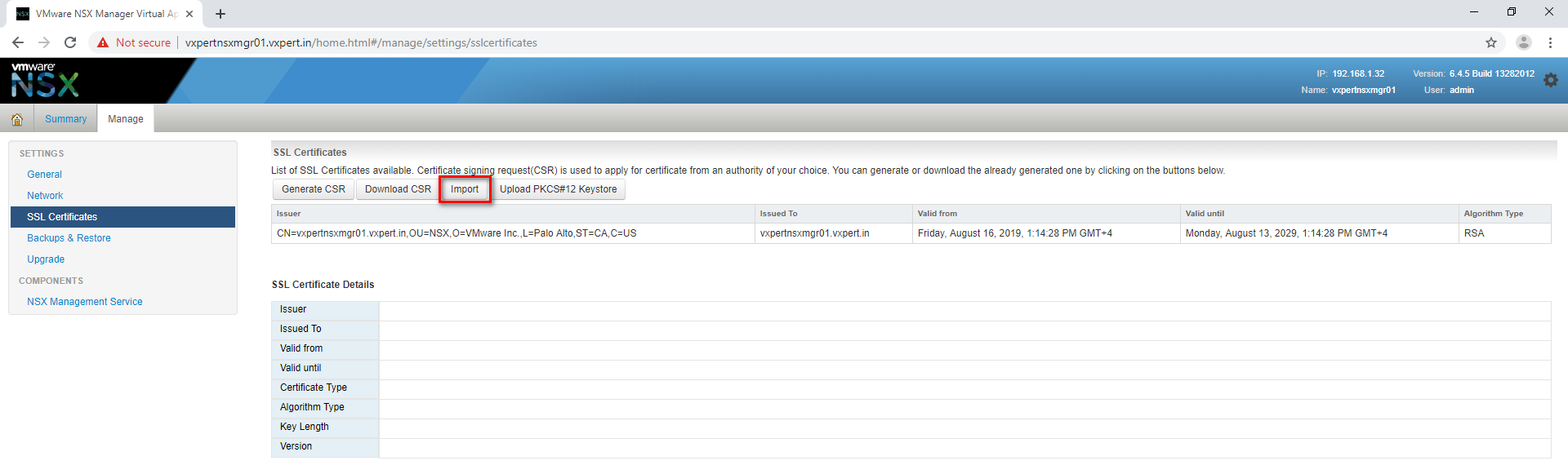
Browse and provide the newly create certificate and click Import
Now you can see the newly imported certificate as shown below
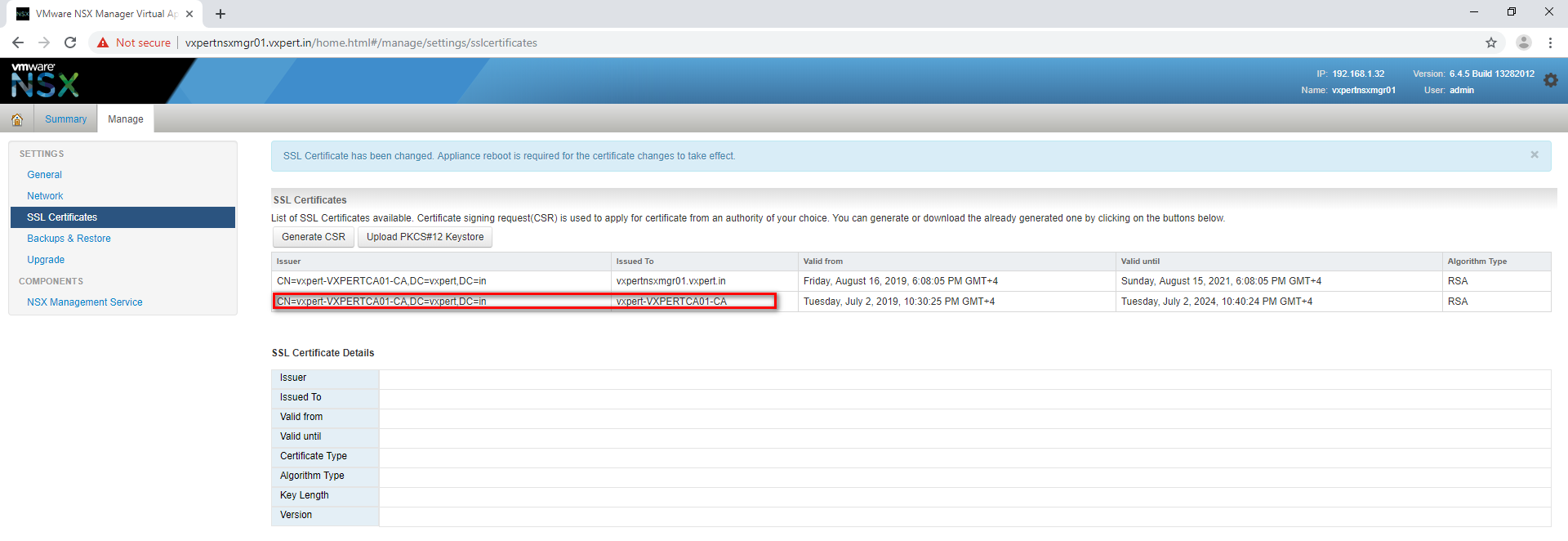
Reboot the NSX Manger appliance to take this chnages on effect
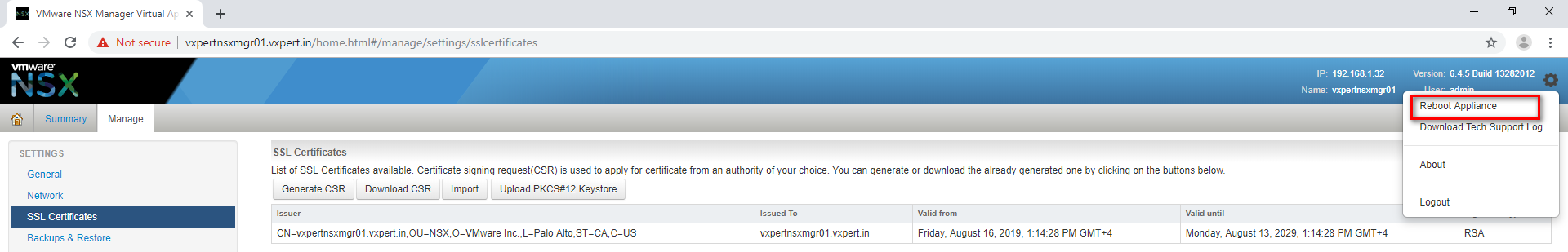
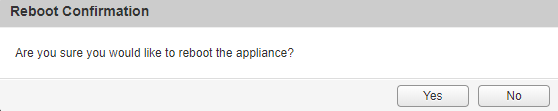
Click Yes to confirm the reboot
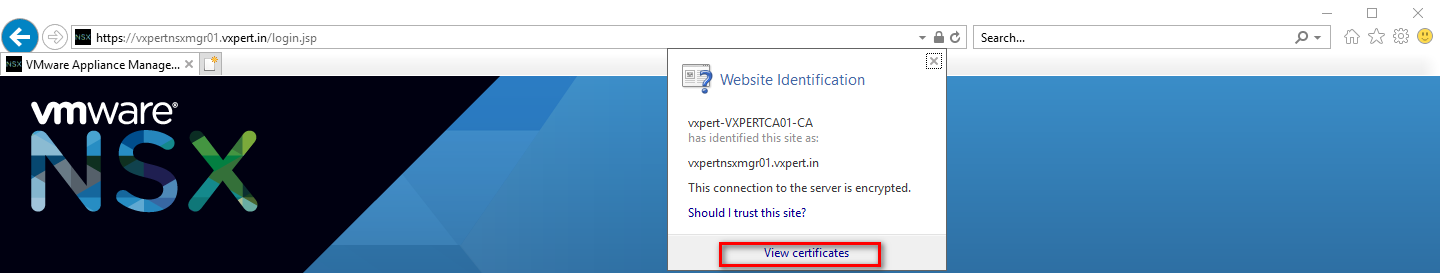
Once the appliance is up, open a new browser session to NSX Manager should now allow you to verify that the CA issued certificate is in operation.
To make this NSX series more understandable, i am splitting this in to multiple blogs
Part 2 – NSX Manager 6.4.x Installation & Configuration
Part 3 – How to Install Microsoft CA Signed Certificate In NSX Manager
Part 4 – VMware NSX 6.4.x Configuration
Part 5 – VMware NSX Logical Switching and DLR Configuration
Part 6 – VMware NSX Edge Configuration
Part 7 – How to Upgrade NSX Manager
Thanks,
If you have any comments, please drop me a line.
I hope this article was informative, and don’t forget to buy me a coffee if you found this worth reading.



Leave a Reply